Although this year has yet to end, some malware has already earned themselves the “deadliest virus in history” of this year. They made the most appearance and inflicted the biggest damage to users worldwide, and as the year has not ended, the cyber community awaits more from them. These are the most dreadful and dangerous malware with a long history of preying on computers and users.
Let’s have a look upon the list of malware that can be considered the deadliest of this year because they truly have the right to be called so.
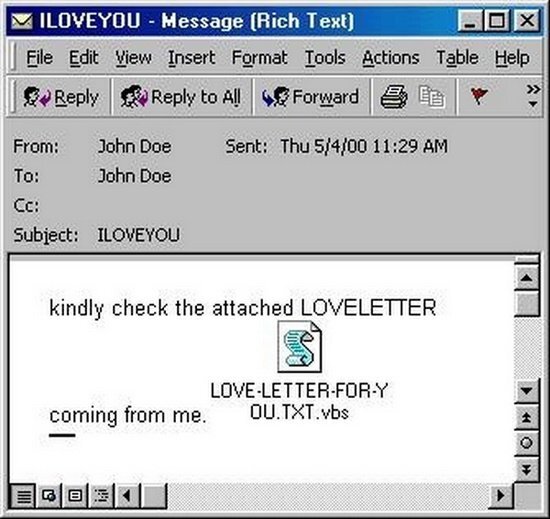
ILOVEYOU virus
This virus – actually, a worm – shows itself to be a very amiable kind of malware. The worm infects victims via email letters that have malicious attachments inside them, a subject line that reads “ILOVEYOU”. The message in the main body of an email goes for “kindly check the attached LOVELETTER coming from me”. Once the victim opens the malicious attachment worm will resend the same email letters to everyone on the victim’s Microsoft Outlook address book.
The infection of the ILOVEYOU virus results in the deletion of MP3, JPEG, and several other file types on the victim’s hard disk. Because Microsoft Outlook is a broadly used email client in corporations across the globe, the worm, by infecting only one person in a company or organization, can spread as fast as any other malware across the entire network. Such behavior was dealing immense damage to companies, paralyzing their work.
Known ILOVEYOU attacks
On May 4, 2000, the ILOVEYOU virus infected 45 million users in just about ten days. Estimated financial losses from that situation reached $10 billion. The spread of infection was extremely quick. Actually, it forced the biggest enterprises like Microsoft, AT&T, and the Ford Motor Company, to stop their work. So did several government organizations – parliaments in the U.K, Denmark, U.S. Army, CIA, and the Pentagon. Getting the situation under control took a couple of days.
ILOVEYOU also comes by the names “love bug worm” and “love letter virus”. As we said, it is not the virus, but a worm that doesn’t need human interaction to spread. Exception is the initial infection – opening the malicious attachment. The worm doesn’t even need to attach itself to any specific software; rather, it spreads via email, specifically using malicious email attachments. When a user clicks on such an email attachment, the virus instantly downloads itself into the targeted system and spreads further across the network.
Conficker
A computer virus attacks the Windows operating system. The virus also goes by the names Kido, Downup, or Downadup. Conficker exploits vulnerabilities in system programs and conducts dictionary attacks. The latter is its way access the administrator accound and spread further to create a botnet. The first time Conficker appeared into sight was November 2008. Since then, it become the most widespread computer infection after the Welchia infection in 2003.
The virus is hard to detect because it uses numerous advanced virus technologies, and therefore, Conficker managed to infect millions of computers globally. But even though it has such an immense scope of infection, it doesn’t cause much damage or harm. The virus doesn’t delete or destroy data, but it only aims to infect as many Windows computers as possible. Specialists assume that one of the reasons why such a successful virus didn’t receive any additional functionality is because its developers had not dared to use it for more purposes in light of worldwide attention.
Analysts also assume that the name of the virus comes from two words. The first part belongs to the English word “configure”. The second one, apparently, comes from the German word “ficker” (“f*cker” in English). But Joshua Phillips, an analyst from Microsoft, gives another interpretation of the name. He suggests that the name of the virus comes from rearranging the domain name trafficconverter.biz parts. Conficker used this domain to update itself in the early stages.
Application and fame
Since its appearance, the virus has managed to target several high-profile entities. It attacked military organizations of different countries, police, and government. In January 2010, Conficker infected the Greater Manchester Police computer network. The police disconnected the affected network from the Police National Computer for three days. That led police officers to switch to old-style paper checks to issue fines to vehicles and people.
On March 24, 2009, Conficker infected the House of Commons computers. The specially issued memo of the UK Parliamentary ICT service warned users. It called them not to connect any equipment to the infected network before the situation gets mitigated.
On February 2, 2009, Bundeswehr, the unified armed forces of Germany, also became the victim of this malware. Conficker successfully infected about 100 computers. The same month and year, Conficker attacked the IT system of Manchester, causing nearly 1.5 million pounds of financial losses. Specialists believe that the initial source of the infection was a USB flash drive, and since then, Manchester has banned their usage.
Another target of Conficker included Intramar, a French Navy computer network, and NavyStar/N* desktops on multiple Royal Navy warships and submarines.
Even though the virus appeared long ago, specialists report that it still infects computers yearly. The virus won’t cause much harm to your device, like data loss. Still, it could significantly affect the performance of your computer, slowing it down and affecting the general work performance as well.
Virus “MyDoom”
This is another computer virus that targets Microsoft Windows. The first time it was detected was on January 26, 2004. Its names also include WORM_MYDOOM and Win32.Mydoom, W32/Mydoom@MM, Mimail.R, Shimgapi, Mimail.R and Novarg. Specialists estimated that the virus is the fastest spreading malware ever. They say it has surpassed even the previously set records by ILOVEYOU and Sobig worm, creating a new record yet to be beaten in 2022.
MyDoom is a worm that spreads via emails that contain malicious attachments. These emails also have texts that read, “andy, I’m just doing my job, nothing personal, sorry”. Once the victim opens the attachment, the worm will spread further by sending copies of an email to email addresses found in the local address book. In the days, the worm managed to infect nearly 500,000 computers globally.
The worm received its name from Craig Schmugar, an employee of the computer security firm McAfee. Schmugar has been analyzing the code of the worm and noticed the text “mydom” which was present inside a line of the worm’s code. In his own words, “It was evident early on that this would be very big. I thought having ‘doom’ in the name would be appropriate”. The very first analysis of the malware brought to the idea that it is one of the variants of the Mimail worm; that’s where researchers speculated that the same developers were responsible for the creation of both malware.
Early, many security firms believed that the worm was a brainchild of Russian hackers. Today, however, the actual author of the malware is still unknown. It appears that the sole purpose of the worm’s creation was to send bulks of spam emails through all infected computers. Still, the case with SCO Group showed another variant of the worm’s actual purposes. MyDoom attacked the American software company with a DDoS attack. This event even gave birth to a hypothesis that it has relations to SCO Group’s lawsuits against Linux. But security researchers rejected this theory. Later the idea law enforcement agencies also disproved this version. Investigation attributed the responsibility for the attack to organized online crime gangs. The worm doesn’t target certain universities and companies as well.
Virus “Stuxnet”
This is a particular virus that ordinary users don’t need to worry about. It targets only critical industries like defense, electrical grids, and power plants. It’s a peculiar feature of this malware – targeting infrastructures rather than money extortions or other typical things. The malware gained its fame in 2010, after Stuxnet had attacked Iran’s nuclear facilitie. Israeli intelligence, the CIA, and the U.S. National Security Agency are believed to have developed the worm. It is the first known malware capable of damaging hardware.
In 2010, at the Iranian nuclear facilities, Stuxnet attacked the programmable logic controllers (PLCs) used to automate machine processes. Reportedly, the malware damaged multiple centrifuges in Iran’s Natanz uranium enrichment facility, making them burn themselves out. Since the famous attack, the worm mutated to create several other similar variants of malware. They can target different kinds of critical industries and energy-producing facilities such as gas lines, power plants, water treatment plants, etc.
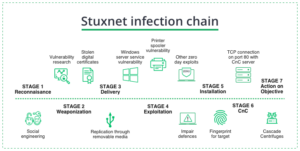
Stuxnet infection chain
Stuxnet is capable of getting on a USB stick and spread via Microsoft Windows computers. For every PC this virus attacks, it performs a scan for Siemens Step 7 software. This electrical equipment monitoring tool acts as a marker for further attack. After founding these computers, the malware receives the update over the Internet and starts sending damaging instructions to the electro-mechanical equipment. To cover its malicious activity, the malware sent fake feedback to the central controller so that the person in charge of monitoring the equipment would not notice anything going wrong.
Although Stuxnet was reportedly set to expire in 2012, the malware has left some legacy behind. Other hackers used its original code to create similar malware like Triton (2017), Industroyer (2016), Havex (2013), Flame (2012) and Duqu (2011).
Virus “CryptoLocker”
This is a ransomware that encrypts your files and demands ransom payments to regain access to the lost files. This ransomware mainly spreads via phishing emails that contain malicious attachments. Usually, cybercriminals disguise these emails to make them look like legitimate correspondence from UPS or FedEx. Users who receive such emails are expected to click on a malicious attachment to initiate the infection. After the successful infection, the victims are asked to pay the ransom. CryptoLocker was mainly active from early September 2013 to late May 2014.
Specialists identified this ransomware as trojan virus (a malicious program that pretends to be useful and helpful). Its targets were computers running different versions of Windows. It was gaining initial access via malicious emails that were disguised as coming from UPS or FedEx. If successful, the ransomware began to look for data and files to encrypt, such as network file shares, external hard drives, USB drives, shared network drives, and even cloud storage drives.
In November 2013, CryptoLocker infected nearly 34,000 computers, mostly from English-speaking countries. Specialists released a free encryption tool in 2014, but different reports say that the ransomware had already managed to extort nearly $27 million before the decryptor release.
Morris Computer Worm
It is one of the oldest self-replicating computer worms that, back in 1988, caused denial-of-service for nearly 10% of the 60,000 machines from the ARPANET. Robert Tappan Morris, a student at Cornell University, wrote this worm. On November 2, 1988, he released the worm from MIT. To spread the Morris Worm used vulnerabilities in UNIX send mail, rsh/rexec, finger, and also guessing weak passwords.
During the infection process, the worm checks if it did not infect it earlier. Still, it can reinfect it again up to seven times to ensure the user could not spoof the worm infection signature. In 1991, court case convicted Robert Tappan Morris under the 1986 Computer Fraud and Abuse Act, which resulted in a sentence of him spending three years in prison.
Computer Virus “Melissa”
Another old-school virus that was active in early 1999. This mass-mailing macro virus targeted Outlook-based systems and Microsoft Word-based systems. At that time, it was the fastest-spreading malware. It actually brought general awareness about all possible damages and risks of unsolicited emails. At the same time, this virus became the prototype for all other kinds of malware. Melissa brought such devastating issues that just a few months after its first-time rampage, the virus creator was arrested and received a sentence in prison.
The Federal Bureau of Investigation (FBI) also started a new national Cyber Division focused on online crimes. The virus managed to infect up to hundreds of networks, among them Microsoft and the United States Marine Corps.
Computer Worm: Code Red
The very first virus to target enterprise networks on a large scale. A virus appeared on July 15, 2001, and attacked computers running on Microsoft’s IIS web server. eEye Digital Security employees Ryan Permeh and Marc Maiffret were the first to discover and research the virus. Riley Hassell discovered a vulnerability this virus used to get into the network. The virus received its name after the researchers drank a Mountain Dew Code Red drink while working with this malware. The worm first appeared on July 13; by July 19, 2001, Code Red had infected nearly 359,000 hosts.
Zeus Trojan Virus
The Zeus Trojan is a collection of malicious programs that can conduct various malicious tasks like collecting sensitive information, spying on you and creating a botnet. In 2011 someone leaked the source code for Zeus; later, much Zeus-based malware was spreading, causing damage. The peak of activity for Zeus was in early 2010, making it one of the most notorious malware ever existed.
Zeus is a Trojan kind of malware, meaning it pretends to be some useful and popular program, but instead, it hides within itself the malicious payload. Zeus has two main ways of infecting its victims — via phishing emails and malicious downloads. In phishing attacks, people received an email that was containing a malicious attachment. In other cases, the Zeus phishing emails contain malicious links to infected websites.
Once the victim clicks either on the malicious attachment or links, the Zeus payload gets downloaded. The malware sometimes may reside in malicious online ads that, once a user clicks on them, the malware downloads itself onto their computer. In addition to these infection vectors, a malicious website infects users with malware when they visit it. besides it also other legitimate-looking malicious downloads exist.
 Is a real RED light for the different kinds of spyware
Is a real RED light for the different kinds of spyware
Initially, cybercriminals’ main purpose in developing Zeus was to steal sensitive banking information. In 2009 Zeus attacked Amazon, NASA, Bank of America, and various other companies/ organizations. Specialists estimated that the malware infected up to 3.6 million computers of all targets at that time. In 2010 the FBI successfully investigated Zeus’ malicious operations, which led to the arrest of over 100 people in Ukraine, the US, and the UK. Before the arrest, the group behind Zeus managed to steal over $70 million from their victims.
Although the malware was stopped, it spawned its predecessors like Terdot, Atmos, Citadel, Cthonic, and even Gameover ZeuS botnet. All of them used Zeus code, and the botnet is based the most on it. Gameover ZeuS botnet was often employed to send phishing emails or spam or, in other cases, to conduct DDoS attacks.