If you are a Windows user, you have certainly encountered .exe files. However, you might have wondered: what does EXE file mean and what is the meaning of file extensions whatsoever? You have also seen files with other extensions. Some of them are more common, while some of them are really rare. Let’s get into it and figure out its purpose.
What does EXE mean whatsoever, as well as other extensions?
File extensions, characters after the period sign in the filename, indicate the file type. So what is a .exe file? This extension stands for Windows Executable File. There are roughly two types of files: data files, read by other programs, and executable files, programs themselves, that can be launched within intended software environments, for example, Windows or other operating systems.
Data Files
Examples of data files are JPG images, TXT text files, AVI videos, etc. Some of them can be read by different programs (MP4 videos, for example, can be opened by various video players,) while some can be opened exclusively by native applications. The purpose of some data files, for example, the DLL libraries, is solely to be used during the execution of the system and its applications.
Executable Files
As for executables, they do not need another program to open them. They are likely compiled into machine code before execution by the CPU. Alternatively, they are scripts – sets of commands executed with the mediation of the system itself. There are many other executable file extensions besides .exe. Examples of executable files’ extensions are BAT (batch files – text document containing system commands executable by DOS, Windows, and OS/2,) APK (Android Package File,) RUN (Linux Executable File), and there are many others, including .exe. The program’s executable files launch by themselves but might require data stored in data files. That is why programs, as they are installed, usually include a lot of accompanying files.
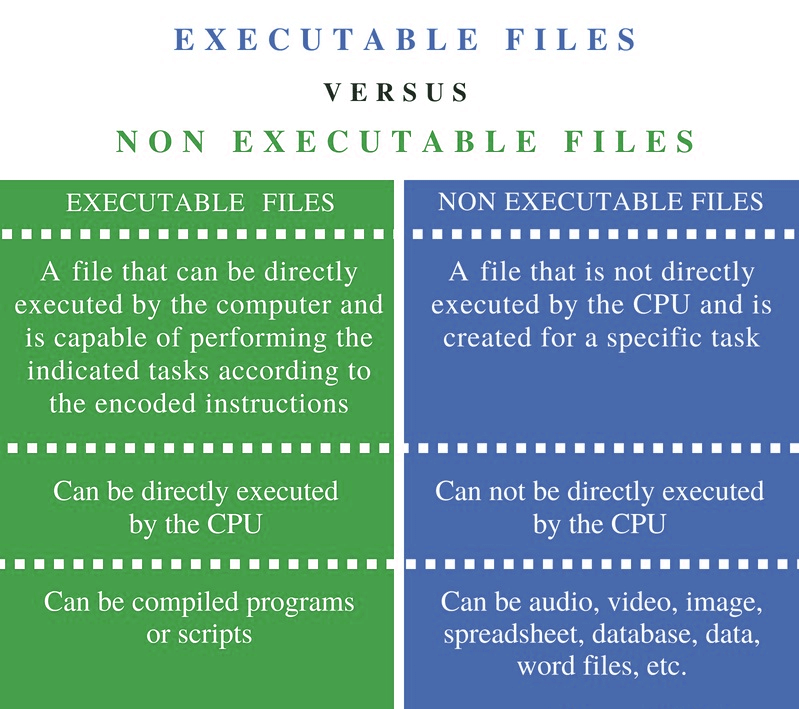
The main differences between data and executable files. Image: Pediaa.com
What is Special About EXE Files?
So, what about the EXE file extension? EXE files (Windows Executable Files) are very common in Windows systems; they are mostly applications or installers of applications. The disputed type of files, .exe files are binary files, which means they are compiled to machine code when they are launched. The executable code these files contain can virtually be of any complexity. EXE files may also contain meta-data, such as icons and digital signatures.
Different EXE file types are intended for various operating systems (DOS, Windows, OS/2, Windows NT, Symbian) and their architectures (32-bit, 64-bit, 16-bit, etc.). Double-clicking the icon of the file will launch it and what happens next depends on the file’s purpose. If it is an installation file, probably called something like setup.exe, the installation wizard will open to proceed with unpacking the program. If it is already an installed program, it will just launch. The name of the EXE file will likely be something like a name of a program: winword.exe (Microsoft Word,) msedge.exe (Microsoft Edge,) chrome.exe (Google Chrome), etc.
Are EXE files safe?
In terms of security, EXE files may raise significant concerns since malware executables can easily be disguised as legitimate programs. Such a type of infection is called Trojan horse. Such malware usually gets onto the attacked machines via untrustworthy downloads. Malicious functions can go alongside desired features of the downloaded program. However, sometimes malware sneaks into the system as a complementary product upon the installation of an utterly different application.
Therefore, before launching an application, or even downloading one, make sure you know whence its originates, who its developers are, and whether you trust them. Also, check advanced options of the installation. It is reasonable to ensure that you are not installing something you do not need. Files with EXE extension can also be parts of different types of malware, not necessarily program-disguised Trojans. Such executables can be parts of complex infections, wherein an EXE file is only a part of a larger malicious scheme.
Avoiding such attacks is possible by vigilance, where these offenses usually happen. Spam through email, social media, and instant messengers featuring attachments and unknown links is the most common way of malware spreading. Considering the plausible look of the spam letters, follow a simple safety rule: never open attachments or follow links found in messages you are not sure why you have got.
Can Antivirus Help?
However, the best way to stay protected against malware, malicious EXE files included, is to have a proper antivirus system. Loaris Trojan Remover, for example, is a lightweight and versatile solution with constantly updated virus databases which speaks for its efficiency. The program has two features dealing with malicious EXE-files and other threats: on-run protection and an antivirus scanner.
- The first function runs in the background and checks the incoming items: downloaded, unpacked, copied from other drives, appearing as the removable drives are inserted. In case a file is recognized as a threat, Trojan Remover will immediately quarantine it and remove or restore it later, depending on the user’s choice. The user will be given suggestions on the file’s possible malignancy. If a file is 100% malware, it will be removed at once.
- The scanner can help if malware was lurking somewhere in the system even before the antivirus was installed. It will also help if attackers somehow managed to inject the malware into the system through a complicated multiple-stage procedure, not by a usual download.
Loaris Trojan Remover does not only rely on databases. It has its own neural network that can recognize malicious activity and determine the files responsible for it.
 Is a real RED light for the different kinds of spyware
Is a real RED light for the different kinds of spyware
Conclusion
In this post, we answered the question: “what is an EXE file?” And these files are neither good nor bad. These are programs all users naturally employ. EXE files are just inseparable from a modern Windows operating system. Malware can come in the form of executable files, but not necessarily with .exe extension. There are anti-malware solutions and safety rules that are good at protecting endpoints.