Browser extensions are a rather useful thing. They make our browsing more comfortable, disabling the ads that can sometimes flood the website so it is hard to read the info you need, as well as create such facilities as the 2FA-assistant or fast notes. But for some strange reasons browser add-ons became an instrument of malware creators, who make money showing users different pay-per-view apps. This article is exactly about such extensions, and also about the reasons for this phenomenon. In addition, you will see the guide for removing these unwanted extensions.
What’s wrong with browser add-ons?
Chrome Web Store has a very little amount of checkings that are required for the application to be added to this platform. It is quite easy to fill it with useless add-ons that can mimic the “helpers” similar to the ones I have mentioned in the previous paragraph. But, as practice shows, users are not going to install the add-ons themselves. There can be a lot of reasons for such a situation, so the developers of trashy extensions decided to distribute their brainchild through the adware.
What can these additional modules do? Likely nothing useful. But usually, add-ons will generate annoying ads, change your search engine, and even substitute your search queries with its own, completely irrelevant result. And, as analysts say, such extensions can easily contain keylogger or stealer functionality, so your confidential information may be compromised. All of these consequences are quite unfavorable, especially when your PC is the main working tool (extremely actual situation in 2020!).
The separate paragraph is needed to describe the joint action of browser add-ons together with Adrozek trojan1. Last is a trojan virus that has an adware behavior. It changes your search queries to its own, which depends on the websites that paid the Adrozek developers for such advertising.
How is it distributed?
Malicious, as one may say, add-ons are distributed by so-called browser hijackers. As it is cleared in their name, their target is to “hijack” your browser, i.e. make it controlled by the algorithm that is inside of browser hijacker. And add-on is an instrument that allows hijackers to take over your browser.
After the virus is injected, it interrupts in your browser work and forces the installation of the extensions from Chrome Web Store. The start of action will not likely be missed – your main page will change its design and the search engine will be changed, usually to Yahoo or Bing. If you try to open Google and search something in it, your search query will be redirected to a search engine that is “chosen” by browser hijacker.
But how have I got this hijacker?
Have you ever used the cracked software? Or, maybe, you clicked the ad somewhere on the Internet? Maybe, you used “free” programs? All of the mentioned cases are the most popular ways of browser hijacker injection. Users who hack the software license-checking mechanism, as well as free software developers also want to be paid for their job. The result of this work is illegal or too unpopular to ask for a payment for this program. That’s why they decide to buy a partnership with the hijacker developers. When you download the staff of the mentioned type, the browser hijacker will likely be inside.
In some cases, browser extensions are offered to install on different websites. Usually, such websites are full of advertisements, have no strict theme and all content on these websites is flooded with different links. They are completely useless as a source of information, but very profitable for its maintainers: hosting of such a website usually costs as a lunch in McDonalds, but the profit from advertising or link crossing is enormous. And only ones who control this website can know what kind of viruses or unwanted programs you can get on their page.
How to remove unwanted add-ons along with the parental viruses?
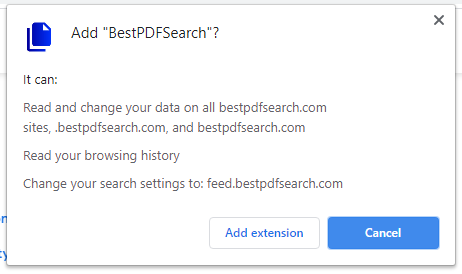
Easy come – easy go. Unwanted add-on installation is quite easy, and the effects of this action is restricted at the infected browser. Hence, it is very easy to remove this threat from your PC without any third-party software usage. Open the browser, and click on one of the active browser extensions that are displayed in the right upper corner. In the appeared menu choose “Browser extensions control”.
You will see the window with the settings of the extension you clicked on. Then, press the arrow at the left side of the settings window. Now, you can observe the list of all add-ons you have in your browser. Delete ones that are not familiar to you.
Do a hard reset
Here is also a more radical method – reset browser settings. Every browser has its own way of being reset, you can see them right below:
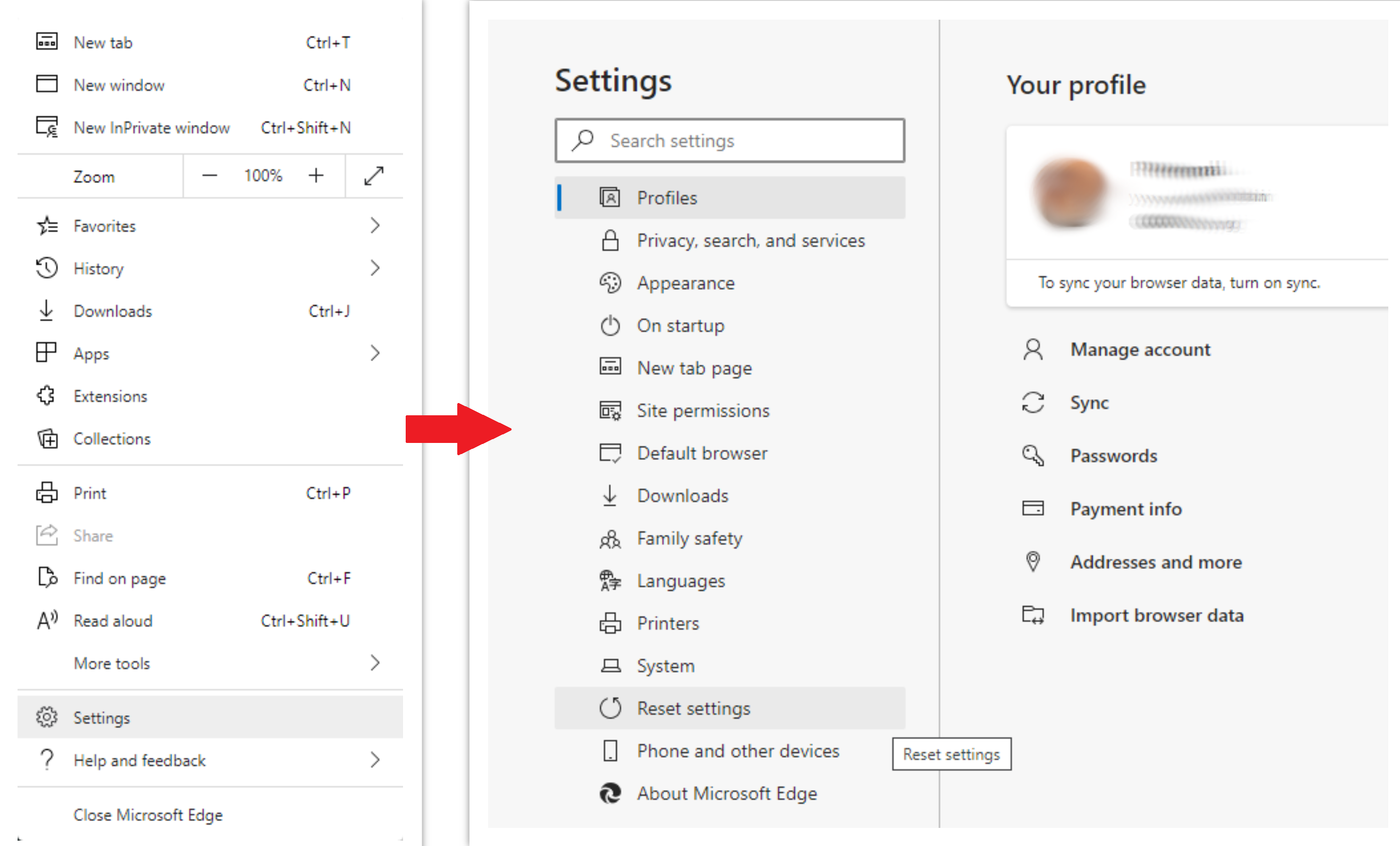
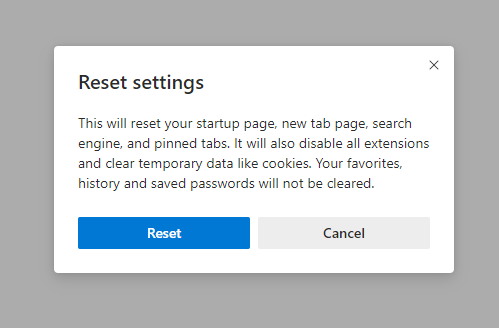
Microsoft Edge
Open the “Settings and more” tab in the upper right corner, then find here “Settings” button. In the appeared menu, choose the “Reset settings” option:
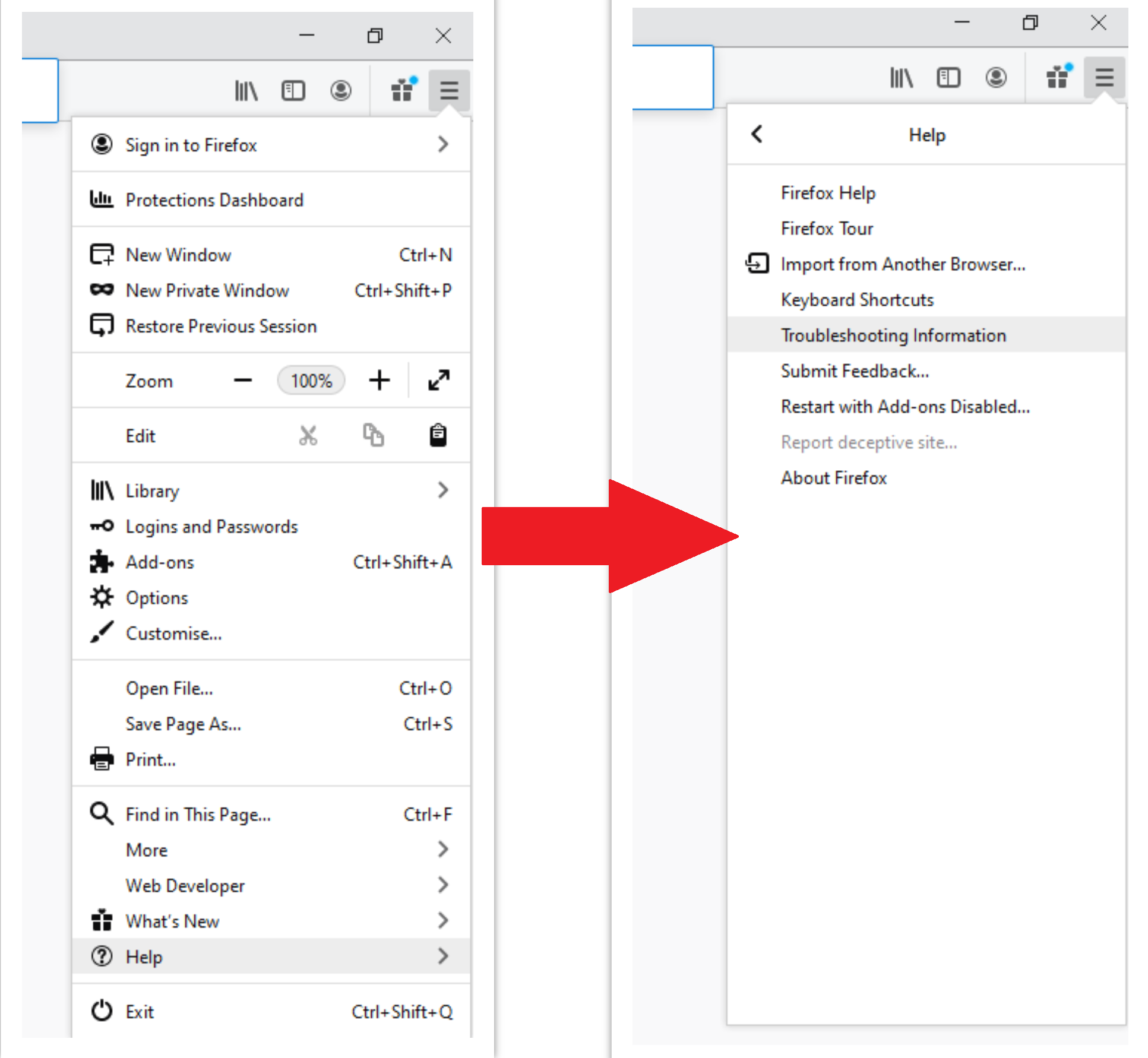
Mozilla Firefox
Open the Menu tab (three stripes in the upper right corner) and click the “Help” button. In the appeared menu choose “Troubleshooting information”:
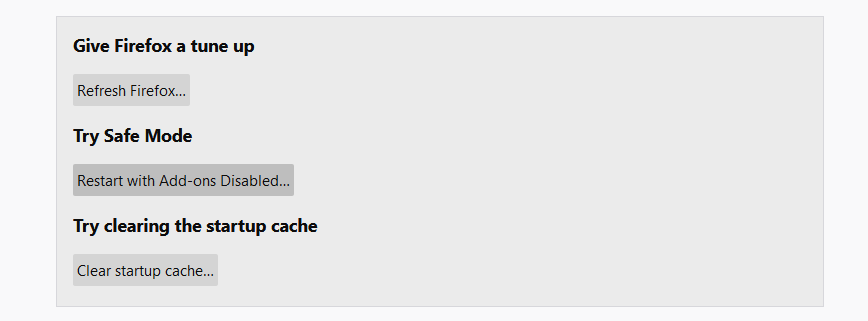
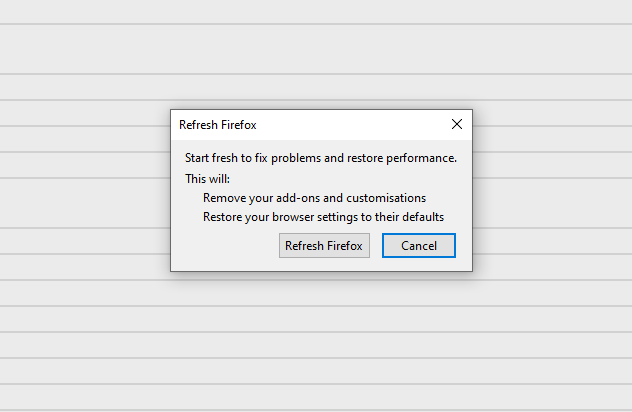
After choosing this option, you will see the next message:
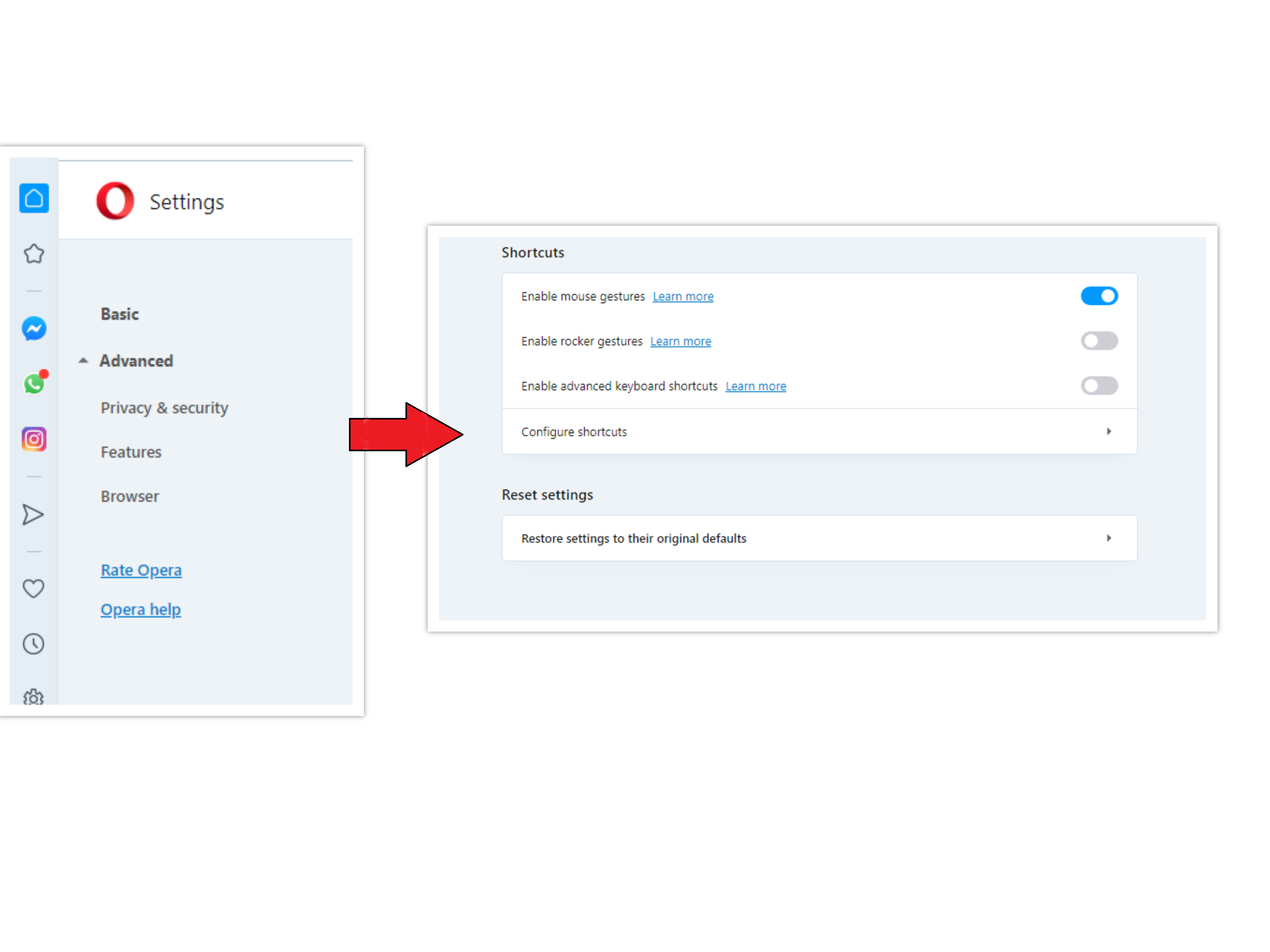
Opera
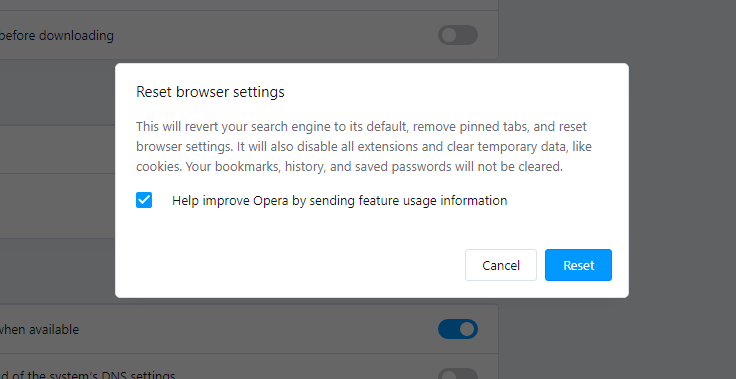
Open the Settings menu by pressing the gear icon in the toolbar (left side of the browser window), then click the “Advanced” option and choose the “Browser” button in the drop-down list. Scroll down, to the bottom of the settings menu. Find there “Restore settings to their original defaults” option:
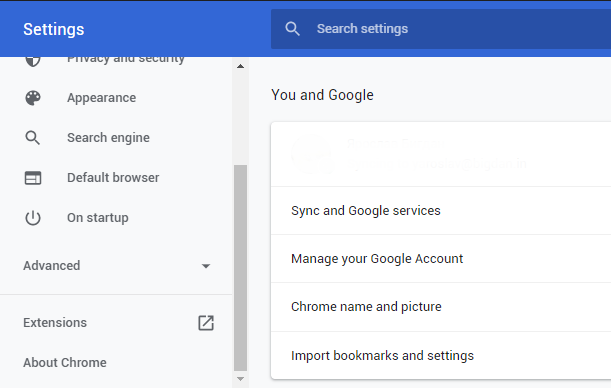
Google Chrome
Open the Settings tab, and find the “Advanced” button. In the extended tab choose the “Reset and clean up” button:
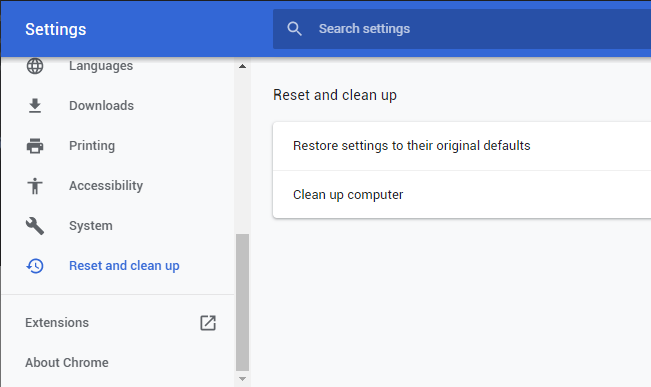
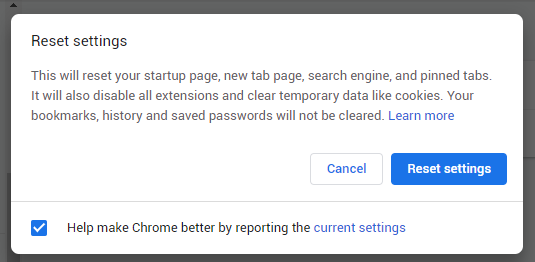
Finally, you will see the window, where you can see all the settings which will be reset to default:
When manual steps are not enough
Besides such easy cases, there are also situations where extensions are added by much more serious virus(es). One of the most common cases is the Adrozek trojan, which was already mentioned in this article. Removing the trojan is a very non-trivial task: this trojan makes a lot of changes in your computer registry, as well as in the DLL files of browsers. Such changes are very hard to revert without specialized programs.
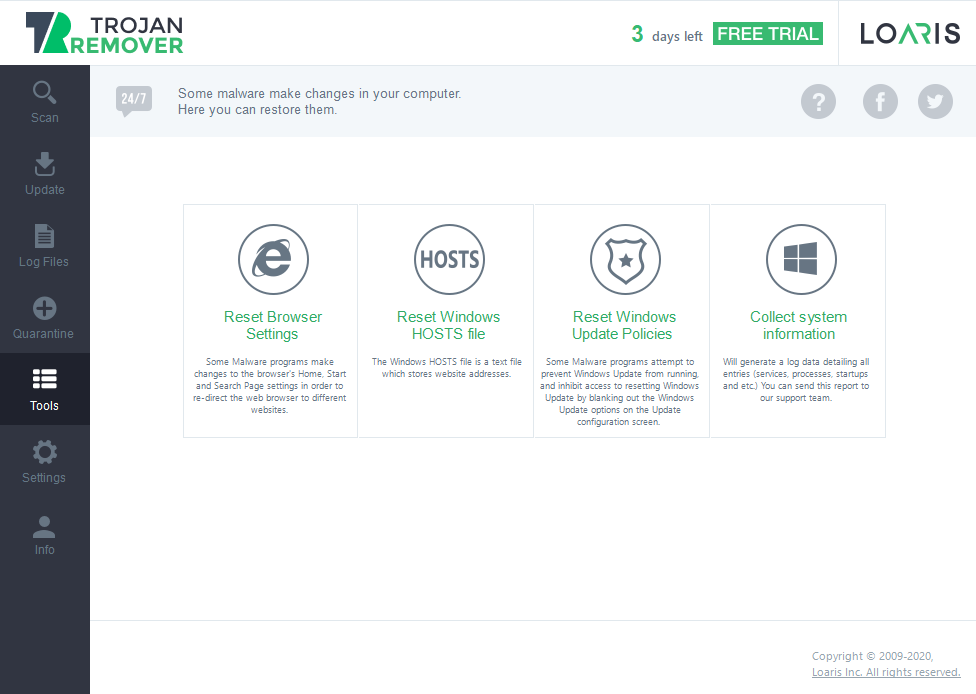
I would recommend you use Loaris Trojan Remover to wipe all malware out of your computer. It has an easy-to-use interface, flexible settings, and a high efficiency of scans. As an addition, it has an embedded Reset Browser Settings function, which can substitute all actions you read above.
 Is a real RED light for the different kinds of spyware
Is a real RED light for the different kinds of spyware
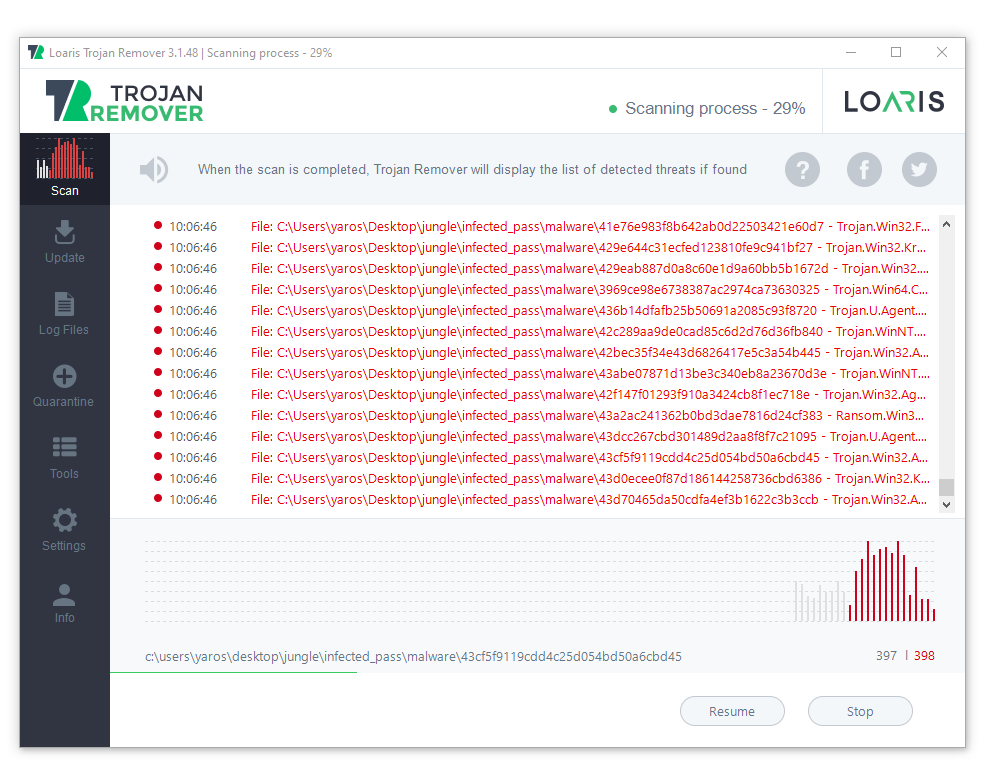
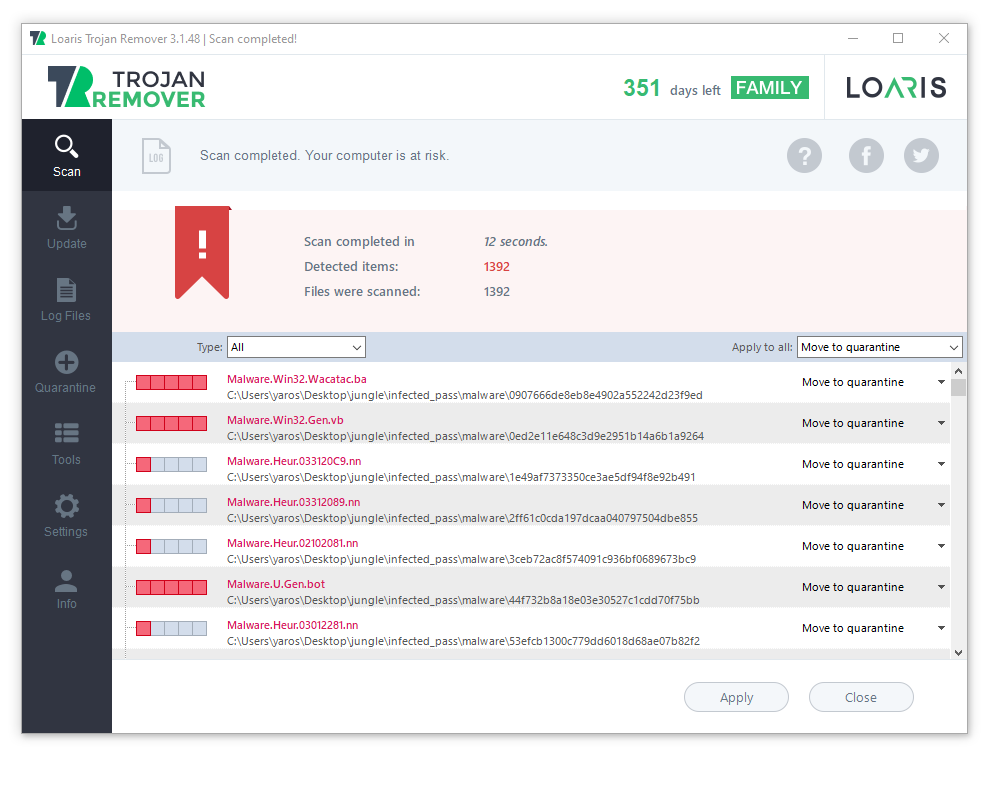
Install Loaris Trojan Remover and run the full scan. It lasts for about 12-15 minutes but allows you to be sure that no malware is left in your system.
As the scan is completed, press “Apply” to delete the viruses from your computer.
To reset the settings of your browser, go to Tools → Reset Browser Settings, and confirm the operation by pressing “Yes”. Your browser will become as good as new.
- About Adrozek virus on the Microsoft website