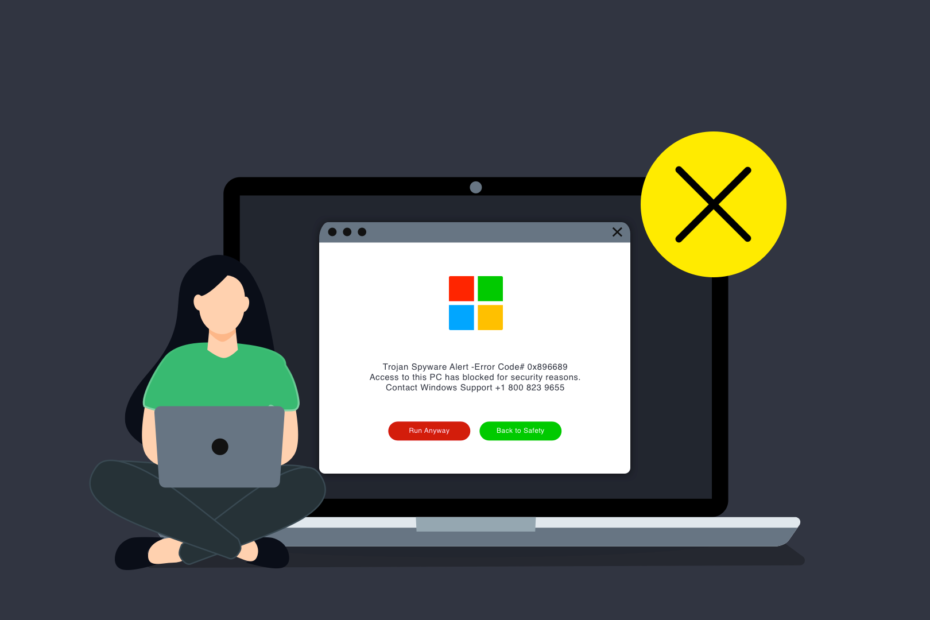
Data Leaks and Data Breaches — Definition and Analysis
Reports about data leaks in large and not-so-large companies have become increasingly frequent lately. Data breaches and leaks refer to unauthorized access or disclosure of sensitive data, which can have severe consequences for the organization and those whose data is leaked. Next, we’ll break down what Data Leaks and Data Breaches are, how these terms differ, and what steps you… Read More »Data Leaks and Data Breaches — Definition and Analysis